Cyber Threat Protection
For today's flexible workforce, your team needs coverage remotely, in the office, and at home. In order to protect mix of networks, infrastructure, and devices, you need dynamic solutions that are proactive and intelligent.

Automation of Security Ops

Advanced Monitoring
From the edge, data centers, cloud and anywhere you need security. Advanced threat intelligence management.

Cloud Driven
Integration with cloud providers, logging options, and native security services that bring all of your security together.

AI/ML Predictions
Proactively improve your security posture and prevent network disruptions before they happen.

NextGen Policies
Application identifiers, signatures, and other advanced ways to identify traffic patterns and threats.
Cloud Network Security At Scale
To increase efficiency and reduce risk of a breach, our SecOps products are driven by good data, deep analytics, and end-to-end automation.
- 8x faster incident investigations
- 44% lower cost
- 95% reduction in alerts
To give you the most thorough application of Zero Trust, we bake it into every security touchpoint
SITUATION
Local government wanted to reduce security complexity, lower security costs, reduce manual policy creation and overlap.
SOLUTION
Consolidate multiple security functions into a single, natively integrated platform, safely enabling users, applications and traffic across endpoints, servers, networks, cloud and SaaS environments.
IMPACT
Decreases capital and operations costs with fewer devices to deploy and manage. Reduces manual work of correlating threats across many devices and point products.
SITUATION
Apply network segmentation for effective protection of mission-critical applications and data in a traditional data center.
SOLUTION
Reduce the ability of attackers to move freely across data center resources; reduce the risk of unauthorized insider access based on user visibility and privilege levels; minimize risk of data exfiltration from the traditional data center.
IMPACT
Minimize exposure by compartmentalizing systems and data belonging to specific applications and/or business units. Limit unauthorized lateral movement into and across the data center.
Get our free report on The State of Cloud Native Security
In these yearly State of Cloud Native Security Reports, more than 3,000 respondents around
the world are surveyed about their cloud adoption strategies, budgets, experiences, and plans.

Cloud Firewall + Endpoint Security Solution

Cloud Firewall
$9/Month/Device
Zero Trust Network Access (ZTNA) 2.0
Fully managed cloud firewall with features for a remote workforce.
- Prisma Access
- Global VPN
- Firewall as a Service (FWaaS)
- Network Encryption
- Cloud Secure Web Gateway

Cloud Firewall + Endpoint Security
$16/Month/Device
All Users, All Apps, Protected Anywhere
Fully protect your end user devices + corporate network for a simple low cost.
- All the features of Cloud Firewall
- All the features of Endpoint
- Managed policies
- Dedicated onboarding specialist
- 24/7 online support
- Unlimited storage space

Endpoint XDR Security
$9/Month/Device
Simplify SecOps
Set the foundation for your device XDR security.
- ML Driven Threat Detection
- Incident Management
- Automated Root Cause Analysis
- Deep Forensics
- NextGen AntiVirus
- Disk Encryption
- Vulnerability Assessments
Need clarification?
What is Cortex XDR?
Security teams face a dizzying array of threats, from ransomware and cyberespionage to fileless attacks and damaging data breaches. However, the biggest headache for many security analysts is not the endless number of risks that dominate news headlines but the frustrating, repetitive tasks they must perform every day as they triage incidents and attempt to whittle down an endless backlog of alerts.
Does endpoint security support my devices?
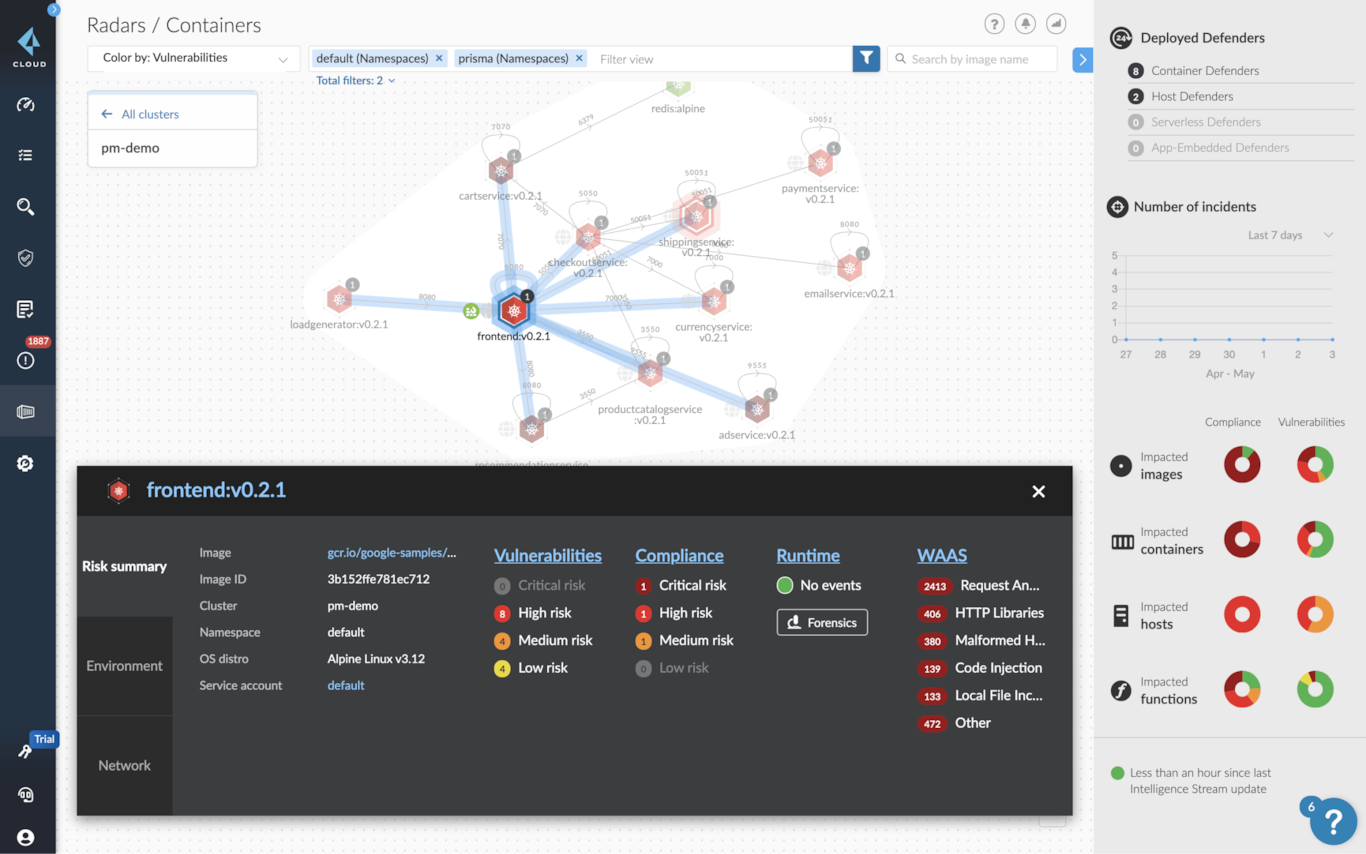
The Cortex XDR agent can be easily deployed to all your endpoints, including your Windows, macOS, Linux, Chrome® OS, and Android® systems, without requiring a reboot. Perfectly suited for physical servers, virtual machines (VMs), and containers, the Cortex XDR agent can protect all your digital assets, from mobile devices to private, public, hybrid, and multi-cloud environments. Cortex XDR supports frictionless Kubernetes deployment, ensuring your security scales along with your cloud workloads.
Can I save on security costs?
You can store log data from Palo Alto Networks Next-Generation Firewalls, Prisma Access, Prisma Cloud, Cortex Xpanse, and the rest of your security infrastructure in Cortex XDR, and reduce your log management and SIEM costs. By eliminating on-premises log storage and additional sensors and enforcement points, Cortex XDR cuts total cost of ownership by 44% on average compared to siloed tools.
Why should I opt for Prisma Access + Cortex XDR or other Palo Alto security offerings?
Siloed detection and response tools force IT staff to deploy additional hardware and software, but they only offer a narrow view of threats, creating blind spots while forcing analysts to gather and correlate clues from multiple tools.
Cortex XDR gives your analysts the secret weapon they need to eradicate elusive threats anywhere in your environment by stitching together and analyzing all your network, endpoint, and cloud data. With Cortex XDR, you can:
• Prevent advanced malware, exploits, and fileless attacks with the Cortex XDR agent.
• Automatically detect stealthy attacks with machine learning and analytics.
• Accelerate alert triage and investigations to increase the productivity of all your security analysts by
revealing the root cause of any alert.
• Quickly contain threats by coordinating response across enforcement points.
• Simplify operations and improve scale and agility with cloud native deployment.
With Cortex XDR, you gain complete visibility across your network, endpoint, and cloud assets, so you can rest assured that all your users and data are secure.
Get notified on new marketing insights
Be the first to know about new B2B SaaS Marketing insights to build or refine your marketing function with the tools and knowledge of today’s industry.





